The smartest attacks do not merely overcome defences, but actually turn your defenders against you. Such is the case with HIV for example, which infects your immune cells as a way to enter the body.
It turns out there is a close electronic analogue to this, with it being possible to design malware which are activated by the process of antivirus software scanning them, and eventually taking control of the antivirus software. This is particularly bad news as by design antivirus software normally has free rein of your system, allowing the software to examine and modify every nook and cranny of your hard drive and RAM.
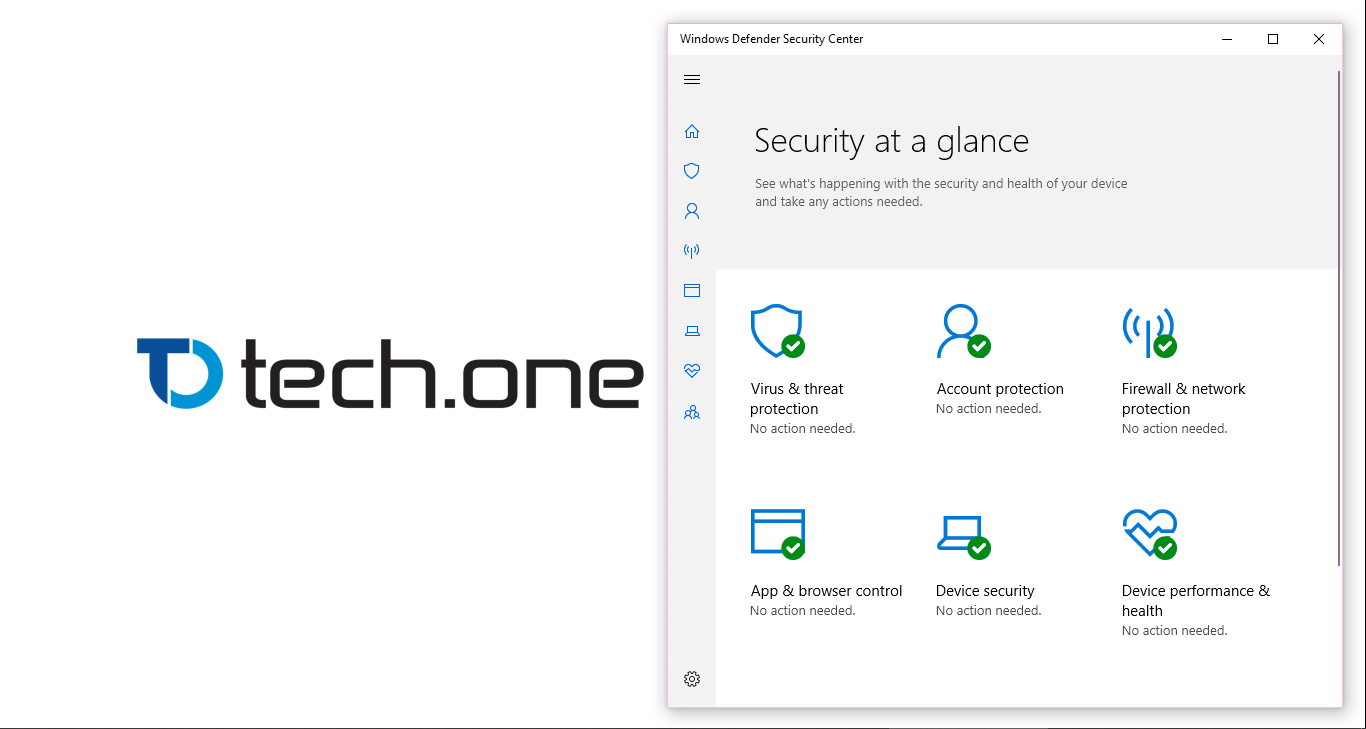
On the Windows Defender Research Blog Microsoft announced that they have found a way to run Windows Defender in a sandbox, meaning even when the software performs the dangerous task of scanning every incoming data stream and is potentially compromised, the software will not be able to adversely effect the rest of your system. Microsoft notes that “Windows Defender Antivirus becomes the first complete antivirus solution to have this capability.”
Microsoft is currently testing the capability with Insiders, but the ability is already built into Windows 10 and Windows Defender and can be activated by:
- Open the Start Menu and type “cmd.exe“.
- Right-click the cmd.exe (Command Prompt app) and click on the “Run as Administrator” option.
- Type setx /M MP_FORCE_USE_SANDBOX 1
- Press enter and wait for the validation.
- Restart the PC.
Read all the gory details at Microsoft here.
Via ZDNet


